As the world turns: So much going on including crowded airports
I got caught in the CrowdStrike outage returning from the LSU Fraud Conference. So much to tell you about that, SolarWinds, and all the great presentations.
There is a lot going on in the world but, for today, I will focus on my small place in it.
I got back late Saturday from Baton Rouge, LA, where I spoke to the LSU Fraud and Forensic Accounting Conference about Hindenburg Research and its short positions in Tingo and Adani. More about those very interesting cases — including my slides — and about all the other fantastic speakers and their slides tomorrow for my paid subscribers.
If you are not already a paid subscriber to The Dig, I'd ask you to consider becoming one so I can continue my work and bring you the amazing work of others.
I was supposed to return to Philadelphia on Friday afternoon but, like millions of others, I woke up Friday morning to find my flights on American Airlines had been canceled. (If you know me you know I don't go anywhere American doesn’t go. I have about 2.1 million miles since 1993 — I joined when I joined KPMG — which gives me permanent Platinum status. It’s one of my few nods to earned elitism. )
As a result, I spent another night in Baton Rouge and got to listen to more presentations including back-to-back wonderful crypto-related presentations by Stacey Ferris, CFE, Assistant Professor of Practice at Virginia Tech's Pamplin College of Business.
Stacey Ferris, in particular had a great presentation before lunch on a taxonomy for classifying digital assets.
Professor Ferris also has a new published paper in the Journal of Forensic and Investigative Accounting with co-authors Drs. Josh McGown, Julie Ravenscraft, and Sean Stein Smith,"Fraud and Unethical Behavior in Cryptoassets: Strategies and Recommendations for Improved Forensic Accounting".
But back to what happened with CrowdStrike, a cybersecurity software company.
The New York Times had a good sum-up:
On Thursday, the tech issues began when Microsoft dealt with an outage on its cloud service system, Azure, which affected some airlines.
Then CrowdStrike sent an update for its software called Falcon Sensor, which scans a computer for intrusions and signs of hacking. If everything had gone according to plan, CrowdStrike’s software would have received minor improvements and customers would have hardly noticed.
Instead, when CrowdStrike’s faulty update reached computers running Microsoft Windows, it caused the machines to shut down and then endlessly reboot. Workers around the world were greeted with what is known as the “blue screen of death” on their computers. Insufficient testing at CrowdStrike was a likely source of the problem, experts said.
As computers restarted themselves over and over, known as the “doom loop,” there was little CrowdStrike could do to fix the problem. Tech staff at affected companies were faced with a choice: walk around to each machine and remove the bit of flawed code, or wait and hope for a solution from CrowdStrike.
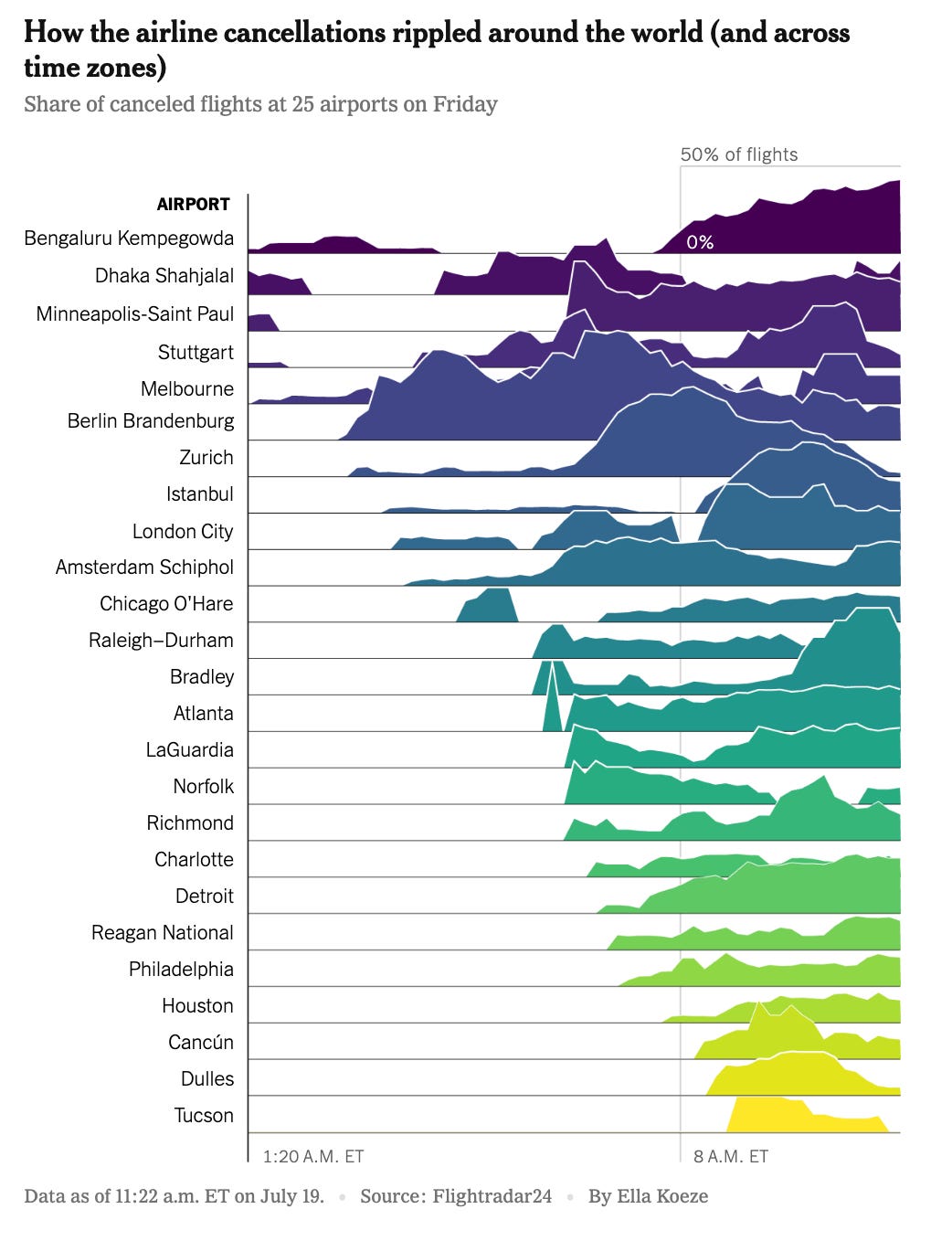
The problems cascaded instantly. At Sydney Airport in Australia, travelers encountered delays and cancellations, as did those in Hong Kong, India, Dubai, Berlin and Amsterdam. At least five U.S. airlines — Allegiant Air, American, Delta, Spirit and United — grounded all flights for a time, according to the Federal Aviation Administration.
The BBC has a great live-blog that tracked all of the impact on airlines. At 11:59 am on Friday London Time, BBC had a blog post on the "blue screen of death":
PC users will know there are a whole host of error messages that can cause panic and frustration.
But those of us who have been met with Windows’ so-called blue screen of death (BSoD) before will feel the pain of those people worldwide seeing it appear today.
It’s what pops up when there is a critical error affecting the operation of your PC – in this case accompanied by an unending loop of trying and failing to restart and launch properly.
A BSoD can be prompted by hardware or software issues, but as Joe Tidy said in an earlier post, it's not the easiest thing to resolve – and can be less easy when dealing with fiddly software bugs.
Even though CrowdStrike says it has identified and fixed the erroneous update bricking Windows devices - those with devices caught in the loop will still need to take their own actions.
Microsoft and CrowdStrike operate in the PC environment and I am a Mac user so I do not usually have to deal with "blue screen of death". In this case the ubiquity of the problem made it a universal problem. Airlines, like banks, still mostly operate in the PC environment and, in some cases, use very old software. (We had another presentation at the LSU conference by a retired IRS fraud investigator, Dr. Robert A. Warren, assistant professor at Radford University, who reminded everyone the IRS still pretty much runs on COBOL.)
Funny, I also saw reports that Southwest Airlines runs on a Microsoft operating system that is so old — Windows 3.1 released in 1992 — that it was barely affected. Cold comfort!
I finally got a flight on Saturday morning, through Charlotte, in probably the last seat available. Baton Rouge airport had been quiet but Charlotte was insane! It was incredibly crowded with blue screens still showing up.

Needless to say I was very grateful when we touched down, quite bumpily, in Philly Saturday night.
This morning I was texting with my friend and frequent collaborator Olga Usvyatsky and she asked if I thought the CrowdStrike outage would lead to additional disclosures and whether companies were vulnerable to SEC actions, given the recent court decision regarding the SEC's complaint against SolarWinds and its CISO.
First, what happened with the SEC and Solar Winds?
Judge Englemayer's ruling is here. I've summarized the judge's decisions.
1. The A[mended] C[omplaint] thus adequately pleads, against both defendants, all elements of its securities fraud claim based on misrepresentations. The Court denies the motion to dismiss as to that claim.
2. The AC thus plausibly pleads scheme liability against Brown based on his dissemination and promotion of the Security Statement. Because Brown's conduct and scienter with respect to the Statement is attributable to Solar Winds, as reviewed above, the AC also ably pleads scheme liability against SolarWinds.
3. The AC separately brings securities fraud claims against SolarWinds and Brown based on other public statements by Brown, including in company-approved press releases, blog posts, and podcasts. AC ,r,r 219-25. The SEC argues that these misleadingly touted SolarWinds' cybersecurity practices.
The challenged statements include:
• In a July 2018 blogpost, Brown wrote: "People often think of security as an insurance policy-something you have to have, like locks on your doors, fire and flood insurance, and business insurance. While these are all true, there are opportunities to think of security as a business enabler, something that can help you open additional doors for your business and stand out from your competition." Id. ,r 54.
• In a March 2019 podcast, Brown stated that SolarWinds was "focused on ... heavy-duty hygiene." Id. ,r 221.
• In a 2020 blog post, Brown stated that Solar Winds "places a premium on the security of its products and makes sure everything is backed by sound security processes, procedures, and standards." Id. ,r 222.
• In an October 7, 2019 press release, Solar Winds stated that it "equips technology professionals with tools to help monitor, manage, and secure today's complex IT environments." The press release included Brown's statement that "SolarWinds is committed to helping IT and security teams by equipping them with powerful, affordable solutions that are easy to implement and manage. Good security should be within the reach of all organizations." Id. ,r 223.
• In a December 12, 2019 press release posted on its website, Solar Winds stated that it was committed "to high security standards, which its partners rely on to help keep the systems they manage secure and compliant." Id. ,r 224. That press release included Brown's statement that SolarWinds and its employees "are always striving to give our partners a leading edge while also fostering a community built on a bedrock of trust," and that meeting security standards "demonstrate[s] a vendor's commitment to privacy and security-something we always strive to improve upon in all we do." Id.
The Court dismisses the AC's claims based on these statements, because each qualifies as non-actionable corporate puffery, "too general to cause a reasonable investor to rely upon them." ECA, 553 F.3d at 206. None of these challenged materials purport to describe SolarWinds' cybersecurity practices or general business practices at the level of detail at which a reasonable investor would have relied on them in making investment decisions. The statements are "too generic to express any objective fact."
4. The SEC also brings fraud charges against the defendants-again under theories of misrepresentation and scheme liability-based on SolarWinds' cybersecurity risk disclosure, originally made in its 2018 Form S-1 registration and incorporated by reference in its ensuing 68 Case 1:23-cv-09518-PAE Document 125 Filed 07/18/24 Page 69 of 107 periodic Form 10-K, 10-Q, and S-8 filings. Based on the same disclosures, the SEC brings a false filing claim against SolarWinds. The Court dismisses all claims based on the risk disclosure.
5. The SEC brings securities fraud and false filing claims based on SolarWinds' December 14 and 17, 2020 Form 8-Ks, in which it disclosed the SUNBURST attack... The Court accordingly dismisses the AC' s fraud and false filing claims based on conduct following SUNBURST.
6. The SEC next brings claims against Solar Winds under Section 13(b )(2)(B) of the Exchange Act for failure to devise and maintain appropriate "internal accounting controls."
The AC alleges that SolarWinds' cybersecurity deficiencies are actionable under Section 13(b)(2)(B)(iii) because(!) the company's source code, databases, and products were its most vital assets, but (2) as a result of its poor access controls, weak internal password policies, and 48 The Court dismisses the A C's claim of scheme liability relating to the post-SUNBURST filings for the same reasons as above. The AC does not allege Brown engaged in an "inherently deceptive act that is distinct from an alleged misstatement." Kelly, 817 F. Supp. 2d at 343. 94 Case 1:23-cv-09518-PAE Document 125 Filed 07/18/24 Page 95 of 107 VPN security gaps, the company failed to limit access to these "only in accordance with management's general or specific authorization," enabling access by external attackers. AC 320-24.
Solar Winds counters that although the Section 13(b )(2)(B) term gives the SEC authority to regulate an issuer's "system of internal accounting controls," that term, as a matter of statutory construction, cannot reasonably be interpreted to cover a company's cybersecurity controls such as its password and VPN protocols. SolarWinds is clearly correct.
In light of the above, the statutory requirement that a public issuer "devise and maintain a system of internal accounting controls" is properly read to require that issuer to accurately report, record, and reconcile financial transactions and events. A cybersecurity control does not naturally fit within this term, as a failure to detect a cybersecurity deficiency (e.g., poorly chosen passwords) cannot reasonably be termed an accounting problem. Cybersecurity controls are undeniably vitally important, and their failures can have systemically damaging consequences. But these controls cannot fairly be said to be in place to "prevent and detect errors and irregularities that arise in the accounting systems of the company." World-Wide Coin Ins., 567 F. Supp. at 750.
The history and purpose of the statute confirm that cybersecurity controls are outside the scope of Section 13(b)(2)(B). Sections 13(b)(2)(A) and 13(b)(2)(B) were enacted as part of the 1977 Foreign Corrupt Practices Act ("FCP A"), amending the 1934 Securities Exchange Act, In re Yesner, 2001 WL 587989, at *33, and together are referred to as the "accounting provisions," Foreign Corrupt Practices Act of 1977, Statement of Policy, 21 SEC Docket 1466, 1468 (Jan. 29, 1981). The FCPA was passed in response to "a pattern of questionable payments to foreign government officers by prominent American corporations." Id. The accounting provisions were enacted "to assure books and records accurately and fairly reflected transactions and the disposition of assets, to protect the integrity of the independent audit, and to promote reliability and completeness of financial information that is disseminated to investors." In re Yesner, CPA, 2001 WL 587989, at *31.
And with regard to Section 13(b)(2)(B) in particular, Congress's explicit purpose, as codified in the text, was to "provide reasonable assurances that, among other things, transactions are recorded as necessary to permit the preparation of financial statements in conformity with generally accepted accounting principles or any other applicable criteria." S. Rep. No. 95-114 at 7 (1977) (emphasis added). Indeed, Congress recognized that because "the accounting profession has defined the objectives of a system of accounting control, the definition of the objectives contained in this subparagraph is taken from the authoritative accounting literature." Id. (citing American Institute of Certified Public Accountants, Statement on Auditing Standards No. I, 320.28 (1973)) (emphasis added). To that end, these provisions require public companies, in addition to filing with the SEC annual and quarterly reports containing detailed financial information, to put in place systems to ensure that the information reported is accurate and complete. Section 13(b)(2)(A) regulates financial recordkeeping. It requires public companies to "make and keep books, records, and accounts, which, in reasonable detail, accurately and fairly reflect the transactions and dispositions of [their] assets." And Section 13(b)(2)(B), at issue here, requires issuers to "devise and maintain a system of internal accounting controls sufficient to provide reasonable assurances" that assets are safeguarded from unauthorized use, that corporate transactions conform to managerial authorizations, and that records are accurate. As evinced by the broader statutory scheme, the internal accounting controls identified in Section 13(b )(2)(B) thus are intended to provide extra assurance of the accuracy and completeness of the financial information on which the issuer's annual and quarterly reports rely.
To state the obvious, cybersecurity controls are not-and could not have been expected to be-part of the apparatus necessary to the production of accurate such reports. The Court therefore dismisses the AC's internal accounting control claim against SolarWinds for failure to state a claim.51
7. The Court accordingly dismisses the disclosure controls claims for failure to state a claim.
My primary interest is in #6 and I have written about this issue.
The judge says: "To state the obvious, cybersecurity controls are not-and could not have been expected to be-part of the apparatus necessary to the production of accurate such [annual and quarterly reports] reports."
This is just ridiculous and the result of the SEC not stating the case and making the connection clearly enough using the right law, SOX Section 404 (a) and (b). But to do that would implicate the auditors for missing the holes in the boat, too.
In the case of SolarWinds, and arguably Tesla, obvious issues that point to material weaknesses in internal controls were not matched by the auditor pointing this out via material weaknesses in internal controls or even critical audit matters.
To summarize, in my opinion the SEC is using Sections 13(b)(2)(A) and 13(b)(2)(B) of the 1977 Foreign Corrupt Practices Act ("FCPA") because they want to leave the auditors out of it. You may get R.R. Donnelley to settle but most will now fight or ask to have cases dropped.
Go back to the SOX drawing board, SEC!
This is my view:
In the morning, I'll talk about Olga Usvyatsky's latest at Deep Quarry that gives an update on 10-K/As between April 1, 2024, and June 30, 2024 and I will make a few comments on the items she highlights for paid subscribers.
I will also comment more tomorrow about all the great presentations from the LSU conference including slides from Stacey Ferris's afternoon one on FTX, Dr. Deniz Appelbaum's on ESG, the SEC's Mike Willis on authenticity, and slides from my own presentation.
© Francine McKenna, The Digging Company LLC, 2024